| ID | Clearing/sanitizing method |
| c | Overwrite all addressable locations with a single character. |
| d | Overwrite all addressable locations with a character, its complement, then a random character and verify. |
| e | Overwrite all addressable locations with a character, its complement, then a random character. |
| f | Each overwrite must reside in memory for a period longer than the classified data resided. |
| h | Overwrite all locations with a random pattern, all locations with binary zeros, and then with binary ones. |
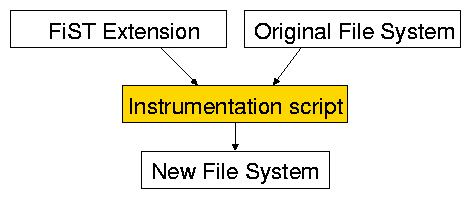
%{
/* print out return values */
%}
%%
%op:all:postcall {
printk("OP_%s: %d (pid: %d)\n",
%op, fistLastErr(), %pid);
}
%%
/* no extra routines are needed */
static int ext2_writepage(struct page *page, struct writeback_control *wbc)
{
return block_write_full_page(page, ext2_get_block, wbc);
}
static int ext2_writepage(struct page *page, struct writeback_control *wbc)
{
{
int fist_tmp_ret_val = block_write_full_page(page, ext2_get_block, wbc);
printk("OP_%s: %d (pid: %d)\n",
"writepage", fist_tmp_ret_val, current->pid);
return fist_tmp_ret_val;
}
}
| File system | Instrumentation | Compilation |
| time (seconds) | time (seconds) | |
| Ext2 | 1.2 | 14.6 |
| vfat | 1.1 | 6.1 |
| msdosfs | 1.2 | 5.8 |
| NFS | 1.3 | 16.5 |
| ramfs | 1.2 | 6.0 |
| Base0fs | 1.3 | 11.7 |